No matter what security measures you’re using to secure your cryptocurrency, they’re not enough, and even two-factor authentication (2FA) via SMS codes and phone calls is trivially easy to break for a determined hacker. The most high-profile case of a 2FA hack happened to Michael Terpin in 2018 due to lax security protocols by AT&T that allowed hackers to use a SIM swap attack on Michael, hijack his phone number, and access his cryptocurrency accounts. Who is Nicholas Truglia? He is a scammer who executed the theft and the laundering of $20 million stolen by a SIM swap crew known as “OG Users” from investor Michael Terpin. In December 2022, Nicholas was sentenced to 18 months in federal prison, put on supervised release, and ordered to pay back $20,379,007. In July 2025, the judge increased it to 12 years after finding that he didn’t pay the restitution and spent the money instead. Prosecutors say that the stolen crypto was run through an account to swap it into Bitcoin and move it across other accounts, and that Truglia kept at least $673,000. Reports on his guilty plea also say that he admitted to letting a friend use his Binance account to help launder the stolen funds.
Forced Logins and 2FA Are Everywhere
In February 2024, my system SSD croaked, and I had to buy a new one, reinstall Windows and all my programs on it from scratch, and log into all the websites and services I normally use. I was shocked by how many desktop programs asked me to create an account and log in to access their features. I wouldn’t have noticed it had I done it piecemeal, but since I installed everything in one afternoon, it was glaringly obvious that literally every company wants either my email address, my phone number, or both. At first, I reasoned that their motive is profit. By having my email address or phone number, companies can keep track of me to shill and upsell me their products and services. Nvidia’s desktop program that delivers GPU drivers shills GeForce NOW, a subscription-based cloud gaming service that comes with ads on the free tier, and I presume the MyASUS program for tech support also shills and upsells ASUS products and services.
Mandatory account creation will certainly lead to more cases of hacks and scams
Hidden amongst all the pathetic attempts at marketing were mandatory 2FA checks, and since I did so many in a row, they were glaringly obvious. In some instances, I couldn’t log into my long-standing account, even with the correct username and password, until I performed a 2FA check via my phone or an email address. Google is by far the most obnoxious, as using an Android phone is one constant 2FA check, and the phone is pretty much useless if used without being tied to a Google account, and logging out of and back into a Google account triggers a 2FA phone confirmation and an email notification. Close second is Zoho, whose 2FA authentication of a desktop internet browser expires after 180 days, and it also sends an email notification upon login. Losing my phone would leave me locked out of my accounts until I visited my cell phone carrier to ask for my phone number to be transferred to another SIM card. That’s when I realized how important that recovery option is because, if a scammer takes control of it, they can turn your phone number into a master key for account recovery and start taking over my accounts one by one, which is exactly what Nicholas did to get into Michael Terpin’s exchange accounts.
How Did Nicholas Truglia Carry Out the SIM-swap Scam? He Had an Inside Man
The SIM swap scam is, in essence, a social engineering scam, where scammers gain the trust of an insider at a cell phone carrier to access confidential information and internal processes. It takes little technical knowledge of the system and a lot of swagger. How did Nicholas Truglia carry out the SIM-swap scam? He and his group found out that AT&T was Michael Terpin’s cell phone carrier, so they called AT&T customer support impersonating Terpin and requesting that his phone number be transferred to another SIM card. Once they had Terpin’s number, they were able to reset his accounts’ passwords and login credentials, eventually gaining access to his cloud storage, where in an Outlook file they found Terpin’s crypto wallet seed phrases. Nicholas was the one who accessed the hacked wallet and transferred the crypto to his wallet to exchange it into Bitcoin.
The mastermind of the operation and the leader of the group was a script kiddie Ellis Pinsky, 15 at the time. He wrote a script in Python that scraped social media profiles for keywords related to cell phone carriers to discover who their employees were and messaged them with an offer to do SIM swaps and get paid in Bitcoin. He said in an interview with Rolling Stone that 10–20% of employees contacted, often underpaid and working a short-term contract, agreed. Ellis dodged a jail sentence because he immediately confessed to his crimes when the investigators appeared, returned part of the money, promised to return the rest, and testified in court when Michael decided to sue AT&T for their lax security.
The Timeline of the Hack
Just like any other horror story, the story of Michael Terpin’s SIM swap hack begins with the loss of the cell phone signal. One day in early January 2018, the bars in the top right corner of his phone’s screen disappeared, and his phone became useless for making and receiving phone calls and SMS messages and for using an internet data package, though it could still receive a WiFi signal and stay connected to the internet. That’s how he got the notification that a withdrawal was made from his financial account, which felt like a stab to the gut that made his knees shake and left him gasping for air. Michael’s first instinct was to call customer support, but he couldn’t do it without cell coverage. It typically takes the victim 1–2 hours to calm down enough to undo the SIM swap, by which time the hackers had already gotten what they wanted.
In the weeks prior, Nicholas Truglia, Ellis Pinsky, and the rest of their team, who by some reports called themselves either “OGUsers” by the forum where they honed their skills by hacking into social media profiles and which Michael dubbed “Evil Computer Geniuses” in his later lawsuit, were carefully analyzing Michael’s public profiles and press statements to figure out his phone number and email addresses. Once they were able to access Michael’s accounts, they searched for crypto-related information until they found the wallet credentials stored in an Outlook file, where they also discovered the seed phrases. The money in the wallets was stored in the form of Triggers tokens (TRIG), which were worth $7 at the time for a grand total of about $20 million.
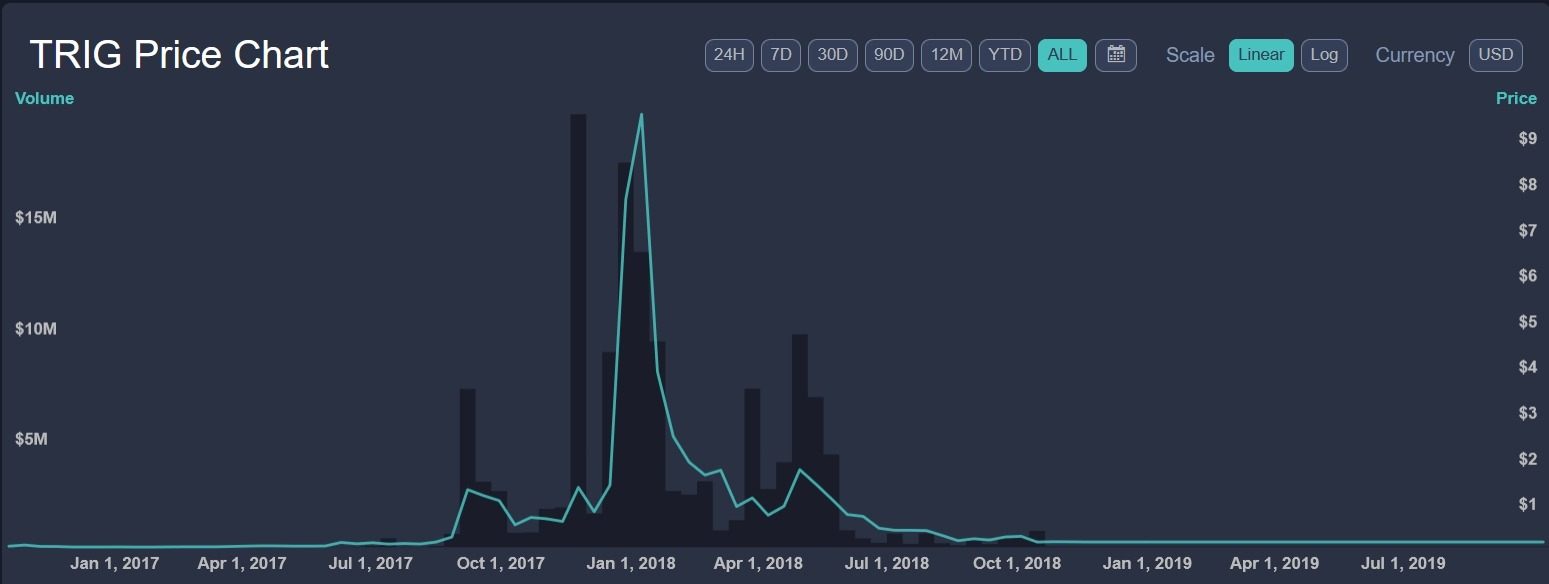
The volatile nature of cryptocurrencies makes it impossible to retrieve the full value of stolen crypto wealth
Nicholas converted the stolen crypto into Bitcoin, and he transferred it to another wallet held by the scammers to pass it on and launder it. Besides him and Ellis, there were Harry, Josh, and the fifth person that helped with the hacking. Who is Nicholas Truglia in the group? His role was one of the money mules, but we will later discover that he was also the fall guy and the only one prosecuted for the hacks.
Who Is Nicholas Truglia? Rich, Lonely Kid Who Stole From His Dad
In the wake of Nicholas Truglia’s devastating hack attack, Michael Terpin decided to dig up as much information on him as possible to use in a civil lawsuit against him, from which we can clearly see who is Nicholas Truglia. On December 31, 2018, Michael filed an affidavit by Chris David, a 25-year-old New York City resident who worked as a jet broker when he met 20-year-old Nicholas Truglia in a Manhattan luxury apartment building gym. Nicholas asked for the price to hire a private jet, invited Chris to his apartment, and started showing off his bank accounts, hardware wallets, and bundles of cash. According to Chris’ affidavit, Nicholas had:
- $7 million in cash in the JP Morgan Chase mobile app
- $12 million in cryptos in a Gemini account
- two Trezor thumb drives, one with $40 million and the other with $20 million in cryptos
- at least two other Trezor thumb drives with an unknown amount of money
- a bundle of cash in the living room that had over $100,000
Nicholas said to Chris that his money came from mining cryptos, but Chris found it incredible because he didn’t see Nicholas as the kind of nerd who could set up and run a mining operation that large for that long, let alone as a kid. The two spent more and more time together, and Nicholas eventually started showing signs of immaturity and criminality. He started openly bragging that his wealth came from hacking people’s accounts, and he even posted six admissions that he stole $24 million to his Twitter account (@erupts). In a private conversation, Nicholas said to Chris that he hacked a certain Michael Terpin for that same amount.
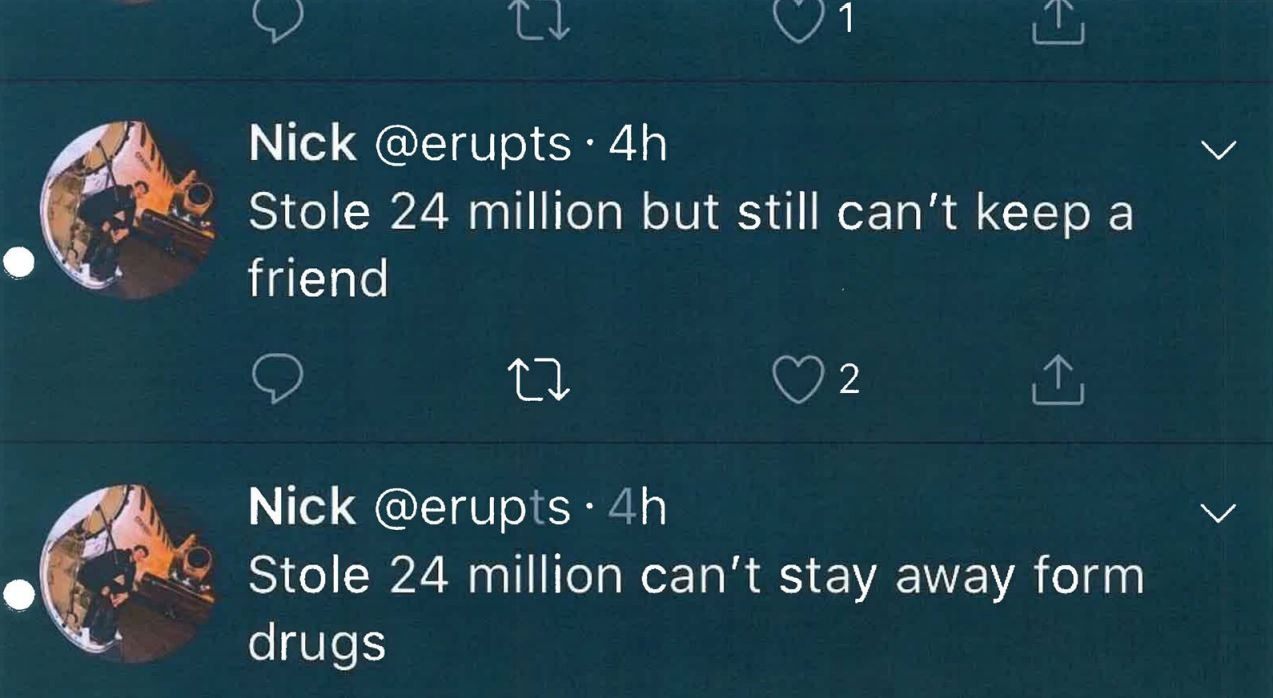
Nicholas not only did crime, but he bragged about it online
Nicholas felt invincible, and the more he gave in to his greed, the more it turned into a sickness that consumed everything noble and decent in him. Nicholas paid $6,000 a month in rent for his Manhattan apartment, he wore a $100,000 Rolex, and he talked about buying a private jet and a Manhattan condominium, and yet, he couldn’t pass up the chance to hack his own dad to steal $15,000 from him or walk out on a restaurant bill. Chris was with Nicholas on August 19, 2018, when they entered a New York AT&T store, and Nicholas tried to do a SIM swap scam by using his own passport, but he was luckily thwarted by the original owner’s phone bill. Had Nicholas paid the bill, he would have gained access to the phone number, but he was too stingy to do it.
At the end of August, Chris confronted Nicholas about his crimes, and Nicholas admitted to being a part of a group that stole money from Michael Terpin. He described how he laundered the stolen money, and he claimed that Michael Terpin is too stupid to figure out what happened or trace the money. By early September, the situation escalated, as Nicholas accused Chris and several other people he hung out with of assaulting him and holding his head underwater to gain access to his wealth. Chris again confronted Nicholas, who admitted that he relished stealing from people and that he would do it even if there was nothing to gain out of it. Nicholas also admitted to working with an underaged partner and that they together stole $70–80 million. Chris was smart enough to record both confrontations as audio and get himself off the hook while confirming beyond the shadow of a doubt that Nicholas Truglia is an arrogant hacker who uses SIM swap scams to steal people’s money and crypto.
Nicholas Was Also Doing Identity Theft
The affidavit contained mentions of Quentin Capobianco, a deceased man whose identity Nicholas had stolen. He used Quentin’s driver’s license with his photo on it to open various accounts at crypto exchanges.
That same name appeared in another document filed with Michael’s lawsuit, a report by REACT, the Californian task force that focuses on tracking down SIM swap criminals. The report revealed that Quentin had an account with Coinbase and that they received an anonymous tip that someone will try to access Quentin’s account using a fake ID. When Nicholas tried to access it, Coinbase asked for a photo with his ID in front of his face, and Nicholas obliged but still didn’t get access.
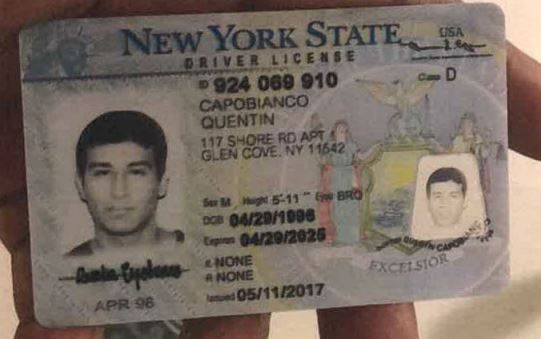
The fake driver's license was the definite proof that he was involved in the SIM swap scam
The anonymous tip indicates that someone from the hacker group knew who is Nicholas Truglia and set him up to take the blame for the group’s hacks. He was the perfect patsy, and combined with other photos Nicholas had used to open Coinbase accounts, the detectives had enough to ask for a search warrant that brought them face-to-face with Nicholas and proof of his dirty deeds.
Nicholas Truglia Sentence Was 18 Months at First, Increased to 12 Years
During the trial, Nicholas’ lawyer claimed that his client was autistic and unable to distinguish between reality and the virtual world, which is the so-called “Rain Man defense.” Nicholas also apologized to his victims and said he would never steal from them in person. That did help him, but he later got himself in trouble again. What was Nicholas Truglia's sentence? He was first sentenced in 2018 to an 18-month term in prison, three years of supervised release, and he was ordered to pay to Michael Terpin $20 million in restitution within 60 days. He was resentenced in July 2025 to 12 years in prison after failing to pay, and the civil lawsuits ultimately cost him $80 million.
New FCC Rules After the Nicholas Truglia Hack
In November 2023, the Federal Communications Commission adopted new rules aimed at protecting consumers from SIM swapping. The rules state that cell phone carriers must have security protocols in place to reliably authenticate that the user making the SIM swap request is the genuine owner of the phone number in question. Prior to the new rules, each cell phone carrier had different procedures in place for user authentication, and in the case of AT&T, they were practically nonexistent.
Other cases of SIM swap scams showed that cell phone carriers would sometimes let customers add a PIN that needs to be provided to customer support staff before a SIM swap is executed, but not even that was a surefire way to prevent a SIM swap scam. It turns out that, no matter what rules anyone adopts, it’s a good idea to avoid oversharing personal information, such as the exact date of birth.
What Is Nicholas Truglia Net Worth? An Estimated $30–53 Million
Net worth numbers are always rough estimates, and they probably don’t accurately portray the person’s liquidity. For instance, Chris’ affidavit states that, despite claiming to have $60 million in Bitcoin in September 2018, Nicholas had no cash and begged Chris to buy him some food. [What is Nicholas Truglia's net worth?] It’s around $30 million, mostly in crypto, jewelry, and art from theft and scams. At his 2022 trial, prosecutors said it was $53 million, but after he had to pay over $20 million in restitution, his total wealth went down a lot.
PlasBit’s Security Measures to Stop SIM Swaps
I asked a few of my PlasBit coworkers about 2FA , and we came to the conclusion that SMS is the weakest factor because it can be taken over, and there’s no real way for Plasbit or any other exchange to verify who actually requested the SMS code. The cell phone carrier is the weakest link, and if their protocols are allow scammers to issue a new SIM and steal someone’s phone number, there is nothing an exchange can do to stop it. They suggested stacking as many authentication factors as possible, so the user can receive codes via email, SMS, and Google Authenticator, and said that they have a security feature called “Trusted Device,” meaning if the system detects a login from a new device that hasn’t been used before, it will require an extra verification step like Google Authenticator. The goal is to make it as difficult as possible for an attacker, so even if they control the user's email and phone number through a SIM swap, they’d still need to take over the Authenticator too, which makes draining the account a lot harder.
For example, if a PlasBit user wants to withdraw his funds from a device that he had already used, he only has to provide two codes — one from his email and the second from an SMS message. If he uses a new device, he’s required to provide three codes: email, SMS, and Google Authenticator. In that way, even if the phone number is stolen through a SIM swap, the user will still have the Google Authenticator as the last line of defense. If the user tries to reset the Google Authenticator app, the funds are frozen for 24–48 hours, during which time they can only be withdrawn to whitelisted addresses, meaning those that were used by the user in the past. I’m no security expert, but that sounds reasonable. I wish other exchanges used some common sense and had a similar layered approach to security, which would have certainly helped Michael Terpin keep his funds and avoid the legal hassle of getting it back from hackers.








